Your iPhone Can Be Hacked Right Now — Here’s How to Protect Yourself from DarkSword
TLDR:
- URGENT: DarkSword iPhone exploit kit has been PUBLICLY LEAKED on GitHub — anyone can download and deploy it in minutes
- Vulnerable iOS versions: iOS 18.4 through 18.7, plus legacy versions 15.8.7 and 16.7.15 — approximately 34% of iPhones and 43% of iPads are at risk
- What gets stolen: contacts, messages, call history, and the entire iOS keychain including Wi-Fi passwords and stored secrets
- Malaysia is a named target region — TechCrunch confirms Malaysian iPhone users are specifically in the crosshairs
- Action required NOW: Update to iOS 26.3 or iOS 18.7.3 immediately; enable Lockdown Mode as an interim shield

The Worst-Case Scenario Just Went Public
This is no longer a theoretical threat discussed in cybersecurity circles. A fully functional iPhone exploit kit called DarkSword has been publicly leaked on GitHub, and security researchers are sounding the loudest alarm they have raised in years. The code is simple HTML and JavaScript — no advanced technical knowledge required. Anyone with basic computer skills can download it, host it on a server, and begin targeting iPhones in a matter of minutes. Your iPhone may already be at risk.
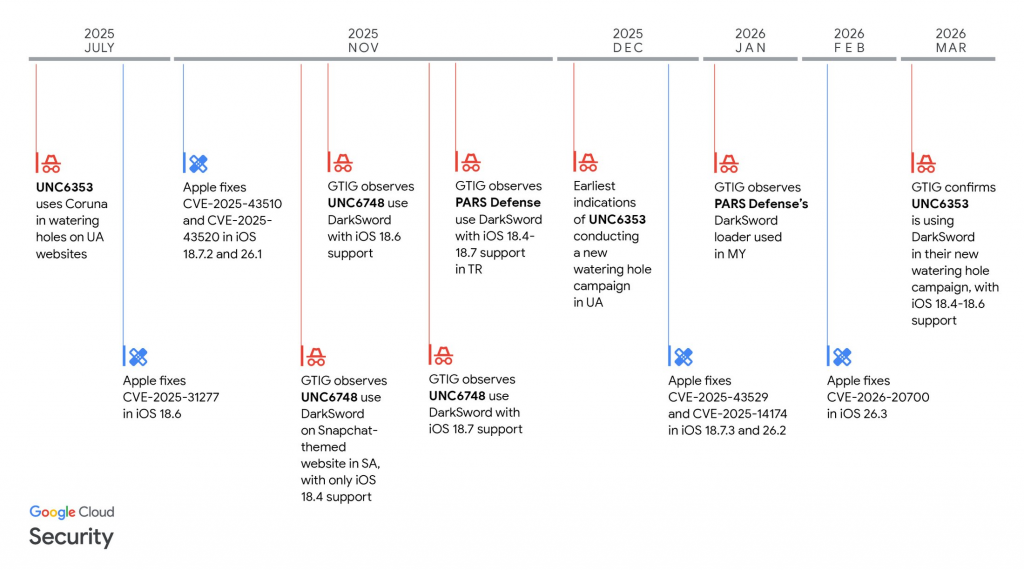
TechCrunch reported on March 23 that a newer version of the DarkSword exploit was published on GitHub, just days after security researchers at Google, iVerify, and Lookout first uncovered the spyware being used in targeted attacks. The original DarkSword campaign was already serious — a sophisticated state-grade hacking tool capable of fully compromising iPhones. But the public release changes everything. “This is bad. They are way too easy to repurpose,” said Matthias Frielingsdorf, co-founder of mobile security firm iVerify. “I don’t think that can be contained anymore. So we need to expect criminals and others to start deploying this.”
The exploit works by chaining together vulnerabilities in Apple’s WebKit browser engine and the iOS sandbox — the security barriers designed to keep apps isolated from each other and from your personal data. A user simply visiting a malicious website in Safari is enough for the attack to trigger silently in the background. There is no prompt, no warning, and no indication that anything is wrong. By the time you notice anything, your data has already been transmitted to an attacker-controlled server.
What DarkSword Can Steal From Your iPhone
Security researchers who analyzed the leaked code describe a chilling level of access. Once the exploit gains a foothold on your device, it begins harvesting a comprehensive snapshot of your digital life. This includes your entire contact list, every text message, your complete call history, and critically — the iOS keychain. The keychain is where your iPhone stores its most sensitive secrets: Wi-Fi passwords, saved login credentials for apps and websites, payment information, and security tokens. All of it can be read and exfiltrated.
The GitHub leak includes code comments written by the original developers that make the scope clear. One comment describes how the exploit “reads and exfiltrates forensically-relevant files from iOS devices via HTTP.” Another outlines the post-exploitation process — once inside, the malware dumps your contacts, messages, call history, and keychain contents directly to a remote server. A separate file references uploading stolen data to a server, confirming this is not just a proof-of-concept — it is a fully operational data theft pipeline.
The targeting is also notably specific. According to TechCrunch’s reporting, Malaysia is explicitly named as a target region in the exploit’s configuration. Combined with the fact that DarkSword was previously linked to Russian government hackers targeting Ukrainian entities, this suggests the tool may have been developed or funded by a state actor before leaking into the public domain. That puts Malaysian iPhone users in a particularly precarious position.
How Many iPhones Are at Risk? Hundreds of Millions
Apple’s own data paints a sobering picture. According to the company’s App Store support statistics, approximately one-quarter of all active iPhones and iPads globally are still running iOS 18 or an earlier version. With more than 2.5 billion active Apple devices worldwide, that translates to hundreds of millions of vulnerable iPhones and iPads. In more specific terms: about 34% of iPhones and 43% of iPads are estimated to be running the vulnerable iOS versions targeted by DarkSword — iOS 18.4 through 18.7, as well as the legacy iOS 15.8.7 and 16.7.15 releases.
This matters because Apple has already issued emergency patches. On March 11, Apple released iOS 26.3 and iOS 18.7.3 to address the vulnerabilities exploited by DarkSword. Devices running these updated versions are protected. But the math is working against millions of users who have not updated yet — and in some cases, cannot update because their device hardware does not support the latest iOS version. Apple also released special security updates for older devices that cannot run iOS 26, specifically targeting the iOS 15 and iOS 16 versions that are still widely used.
How to Protect Your iPhone Right Now
The first and most critical step is to check your current iOS version and update immediately. Go to Settings → General → Software Update on your iPhone. If you see an update available, install it without delay. If your device supports iOS 26, you need to be on iOS 26.3 or newer. For older devices that max out at iOS 16, make sure you have received Apple’s specific security update for that version. Keeping your software updated is, as Apple stated, “the single most important thing you can do to maintain the security of your Apple products.”
If you are unable to update immediately, Apple recommends enabling Lockdown Mode as an immediate interim measure. Lockdown Mode is a feature Apple originally built to protect high-risk users such as journalists, activists, and executives from state-sponsored spyware. It severely restricts how your iPhone operates, blocking many attack vectors including the WebKit exploits that DarkSword relies on. Apple confirmed to TechCrunch that Lockdown Mode will block these specific DarkSword attacks. To enable it, go to Settings → Privacy & Security → Lockdown Mode and turn it on.
Our Take
The release of DarkSword on GitHub marks a grim milestone in mobile security. We have officially entered an era where a zero-day iPhone exploit can be cloned and deployed by anyone with a modicum of technical confidence — no nation-state budget required, no elite hacking team necessary. What was once a tool reserved for sophisticated state actors is now effectively in the public domain, and the clock is ticking for every unpatched device.
The numbers alone are staggering. Hundreds of millions of active iPhones and iPads are running vulnerable software right now. Apple’s emergency patches are available, but patch deployment at this scale is a marathon, not a sprint. Users do not update immediately — it is a fact of human behaviour that security researchers have long grappled with. The GitHub leak essentially gifts opportunistic attackers a window of opportunity that could stretch for months.
For Malaysian iPhone users specifically, the situation demands extra urgency. Malaysia has been named as a target region, which means the threat is not abstract or statistically distant — it is pointed directly at this community. If you are running an older iOS version, your device could be compromised simply by visiting the wrong website. That is a fundamental shift in risk profile for everyday users. The path forward is clear: update your iOS today, enable Lockdown Mode if you cannot update yet, and treat any unusual behaviour on your iPhone — unexpected battery drain, unfamiliar apps, unexplained data usage — as a potential warning sign. DarkSword is out of the box. There is no putting it back.
Keyword: DarkSword iPhone exploit
Source:
• Android Authority — DarkSword iPhone exploit leaked on GitHub
• TechCrunch — Someone has publicly leaked an exploit kit that can hack millions of iPhones